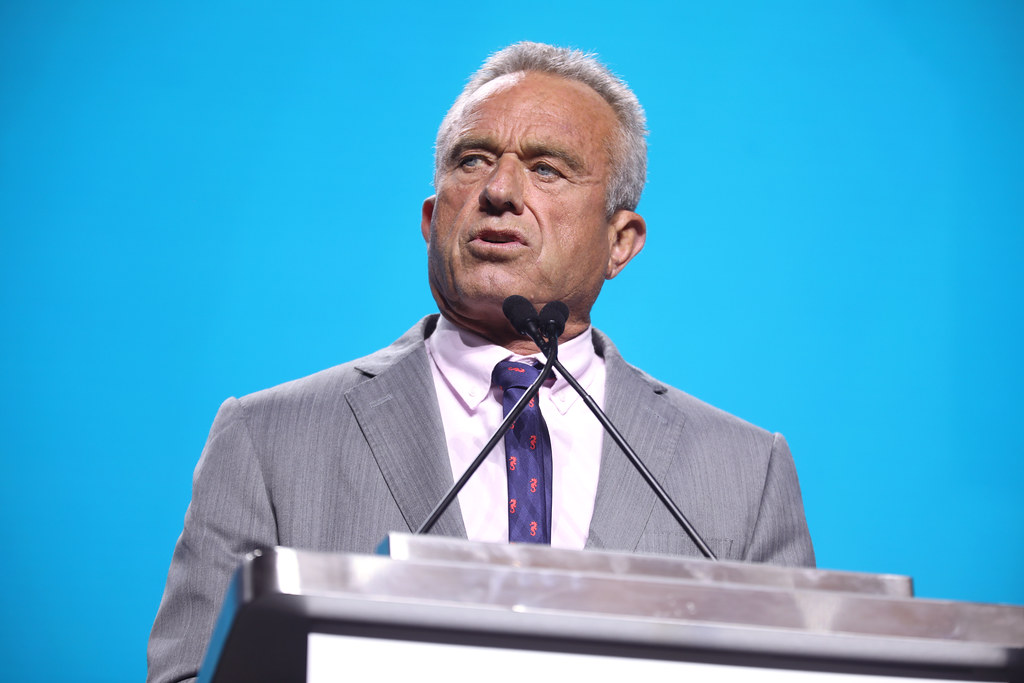
Tandon Professor Discovers Faults in iPhone Fingerprint Sensor
Tandon professor Nasir Memon, along with other researchers, found that smartphones’ fingerprint authentication systems can be hackable through a master print, which has many users’ partial fingerprints.
April 17, 2017
Hackers can’t keep their hands to themselves — and it appears that doing so makes it easier to accomplish their mission.
Researchers from NYU’s Tandon School of Engineering and Michigan State University recently published a paper revealing its discovery of a flaw in smartphones’ fingerprint authentication systems that could potentially allow hackers to access stolen smartphones using a fake fingerprint.
Tandon professor Nasir Memon, one of the authors of the paper, ascertained from Apple’s patent on identity-authentication software that fingerprint identification only used partial fingerprints. He then hypothesized that a fake fingerprint — called a master print — could be constructed that matched a large number of users’ partial fingerprints.
“The home button is small, so it doesn’t capture your entire fingerprint – it only captures a small portion,” Memon said. “Instead of exactly matching your complete fingerprint, you have to just match any one of the partial fingerprints to get in so there’s an opportunity to try and construct fake fingerprints that run off this partial fingerprint. We just took digital prints and tested in a simulated environment and we found out that it was possible to create these master prints.”
Memon said that he became naturally curious about this topic over the course of normal research proceedings.
“We were curious as to how fingerprint recognition worked, because when you enroll it’s kind of like drawing this little picture, then you wonder ‘What the hell is going on? What is it doing?’” Memon said. “Because they’re getting partial impressions, you’re missing a part of the fingerprint, but based on that it’s giving the impression that it captures the whole thing.”
Memon said that he contacted an employee from Apple Incorporated to see if they could help guide his research, but was rejected, so he had to base his research off their fingerprint identification patent.
“I called up somebody that works at Apple and they refused to tell me what to do because it was proprietary information,” Memon said. “So then we looked up the patent and that started giving us a better idea of what we could be doing.”
Memon conducted the study with the help of Tandon graduate student Aditi Roy. Roy was responsible for the actual running of the experiments and the creation of a version of the algorithm used in the study. Roy said that the master prints that they created had a significant and unexpectedly high success rate.
“We used a dataset of 8,200 partial fingerprints. We developed an algorithm to generate synthetic master prints,” Roy said. “With these master prints, we were able to attack 26 to 65 percent of users, depending on how many partial fingerprint impressions were stored for each user and assuming a maximum number of five attempts per authentication. We expected that master print will be able to attack other users. But we were surprised with the high matching capability of the master prints.”
Roy said that this security flaw was troubling because fingerprint authentication is increasingly being used in financial transactions, and that identity theft and issues relating to malicious access can lead to unprecedented financial damages. Roy also said that fingerprint-based authentication systems’ vulnerabilities can undermine the public’s faith in using biometric solutions, which provide an analysis of people’s behavioral and physical characteristics.
“Making these fake fingers, trying this out, it’s not what your little brother or some common criminal can do,” Memon said. “Someone will have to steal your phone to take it away to get to a place where they have fake fingerprints, and try to use the fake fingerprints carefully.”
Memon also said that normal people don’t need to worry about their fingerprint sensors being hacked, but that vendors should understand that their security systems may not be as effective as they thought because of this type of hack. Memon said the risk users face could possibly be reduced by simply changing to the frequency with which iPhones request PIN identifications.
“One way to address this problem is to ask for the PIN if the phone has been idle for a good length of time,” Memon said. “Instead of just after the phone has been turned off and on, the PIN should be requested if the phone has been idle for two hours, three hours, and the fingerprint should not be allowed to unlock it.”
Email Herman Lee at [email protected].